Supersuso Ransomware Removal Guide for Windows (Free Instructions)
Herbie Vance
Issue:I can't open my files, they're encrypted!
I'm panicking right now! I can't open any of the files on my computer! All of them has also been renamed with ".ICQ_SUPERSUSO".
Please help me! I'm desperate!
The Supersuso ransomware is designed to encrypt the files and data in a victim’s computer. Once the encryption process is complete, it will then demand a payment from the victim to unlock their files. Supersuso is one of the many ransomware that uses this kind of tactic. Cybercriminals develop more and more types of ransomware every day for their monetary gain.
Victims are informed that their data and files have been encrypted through the ransom demand message. The note urges the victim to contact the cybercriminals via the ICQ messaging program to begin the decryption process. If victims do not contact the attackers within 72 hours, all of their personal data and will be sold on the deep web. The notice also contains cautionary statements about acts that could result in permanent data loss.
Decryption is impossible in most ransomware infestations without the help of cybercriminals except for those mediocre malicious programs. It is strongly advised to avoid contacting these cybercriminals, as victims frequently do not obtain the decryption tools despite doing so.
Supersuso ransomware will not encrypt any more files once it is removed from the operating system. Unfortunately, removing the virus will not restore any files that have already been encrypted. If a backup was made and saved elsewhere, the only option is to retrieve them from it. To avoid permanent data loss, it is generally advised to retain backups on removable or cloud storage.
Supersuso Ransomware Distribution Method
Most types of online threats, such as Supersuso Ransomware, are disseminated through questionable download sources such as peer-to-peer sharing platforms, websites, and so on. They can also get into a victim’s computer by showing fake updates and illegal activation tools.
By instead activating licensed products through legitimate means, “cracking” tools can cause infections. Infecting systems with fraudulent updaters involve leveraging old program weaknesses and installing malicious software.
Malware can also be distributed via spam email campaigns. Infectious files may be linked inside the fake emails. These files can be disguised as Microsoft Office documents, PDF, executable files, scripts, and more. The infection chain is started when these files are clicked or open, whether intentionally or accidentally.
| THREAT NAME | Supersuso virus |
| Type of Threat | Files Encryptor, Cryptocurrency Virus, Ransomware |
| Encrypted Files Extension | .ICQ_SUPERSUSO |
| File Extension | .lyli |
| Name of Ransom Note | #Decrypt#.txt |
| Amount of Ransom | Not stated, but the cybercriminals threatened on selling the victim’s information to the dark web if they are not contacted within 72 hours. |
| Contact Details of Cyber Criminal | ;@supersuso (ICQ) |
| Threat Symptoms and Potential Damage | Users will not be able to open the files on their system (locked files), file extensions will be replaced to .ICQ_SUPERSUSO. Users will be left with a ransom note by the ransomware developer and will be demanded to pay a certain amount to recover the victim’s files. |
| Method of Distribution | Malicious ads from untrustworthy websites, downloaded torrent files from unreliable websites, Macros or Infected email attachments |
| Suggested Removal Tool | If you think there is an infection in your system but have not yet seen the symptoms in your system, cyber security experts recommend using iolo System Mechanic to perform a holistic scan on your computer. |
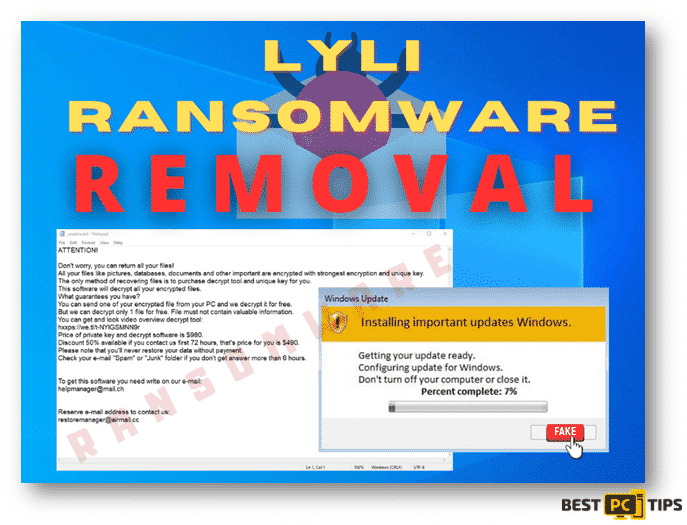
Here’s the content of Supersuso Ransomware ransom message.
“Hello my dear friend
Unfortunately for you, a major IT security weakness left you open to attack, your files have been encrypted
If you want to restore them, install ICQ software on your PC hxxps://icq.com/windows/ or on your mobile phone search in Appstore / Google market ICQ
Write to our ICQ @supersuso hxxps://icq.im/supersuso
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
We are always ready to cooperate and find the best way to solve your problem.
The faster you write, the more favorable the conditions will be for you.
Our company values its reputation. We give all guarantees of your files decryption
IF WE DONT SEE MESSAGES FROM YOU IN 72 HOURS – WE WILL SELL YOUR DATABASES AND IMPORTANT INFORMATION TO YOUR COMPETITORS,AFTER YOU WILL SEE IT AT OPEN SOURCE AND DARKNET
tell your unique ID”
Here’s is a screenshot of how infected files will look like:
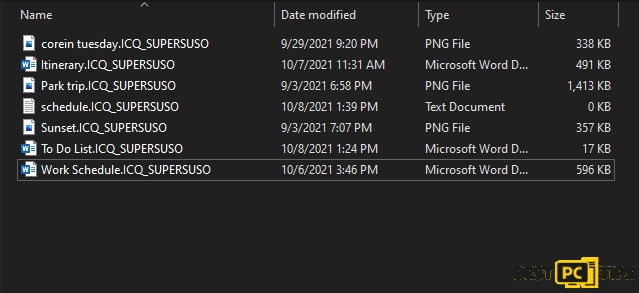
When encrypted, no matter how hard you try or what methods you use, you will not be able to use these files.
How Can You Avoid Being Infected With Supersuso Ransomware?
It is recommended that only official/verified sources be used for downloading. All programs must also be activated and updated using tools given by legitimate developers. Suspicious or unrelated emails should not be clicked especially if they contain attachments or links.
It is critical to have a reliable anti-virus/anti-spyware program installed and kept up to date. This software must be used to scan the system and eliminate threats on a regular basis. If your machine has already been attacked by Supersuso, we recommend performing a full system scan with iolo System Mechanic remove the ransomware automatically.
Automatic Malware Removal With iolo System Mechanic
iolo System Mechanic is a good option if you don’t want to deal with the stress and inconvenience of manually removing viruses. It’s a virus detection and removal and system optimization utility that not only keeps your computer safe from internet dangers but also maintains your computer whole system, including drivers, up to date.

What Should You Do When Infected with Supersuso Ransomware?
If you happen to notice that your computer is infected with the Supersuso Ransomware, you have to make sure that it does not spread to other devices in your network. To do this, you have to isolate the infected device away from the other devices that are connected to your computer and the network.
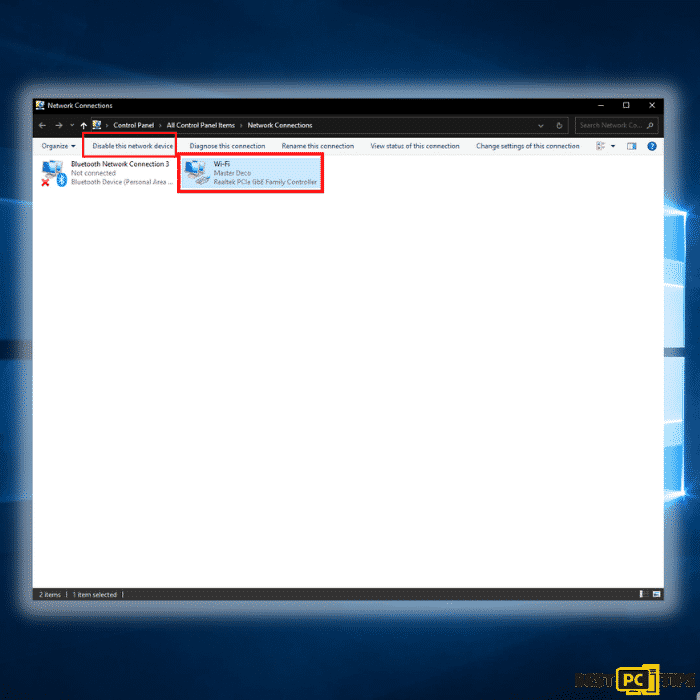
Disconnect from your network (disable the internet)
Step 1: Hold down the “Windows” + “R” keys and type in “ncpa.cpl” in the run command line and click “OK”
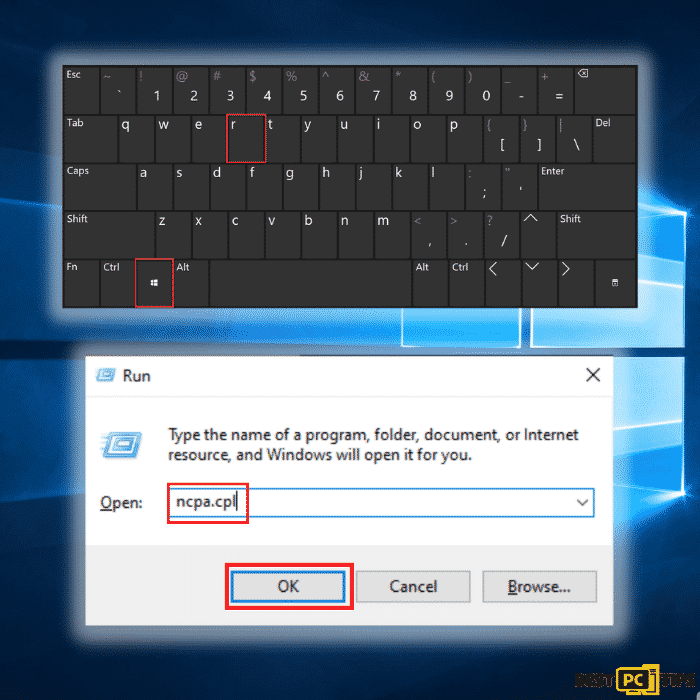
Step 2: Click on the network that you are connected to and click on “Disable this network”
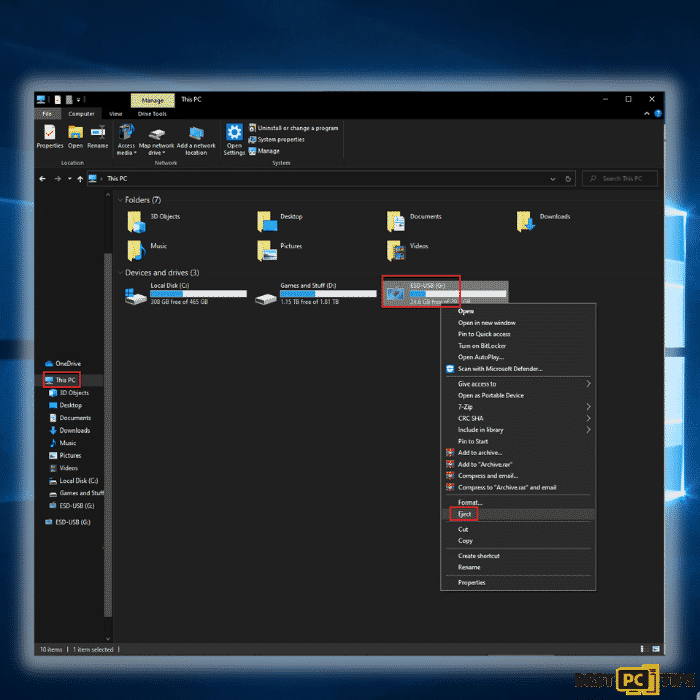
Unplug All Connected Storage Devices from the Computer
The Supersuso ransomware, as previously stated, encrypts data and infiltrates all storage devices attached to the computer. As a result, all external storage such as external hard drives, flash drives, and other similar devices should be detached as soon as possible. To avoid data corruption, we strongly encourage you to remove each device before disconnecting.
Step 1: Open “This PC” and locate all the connected storage devices. Right-click on it and click “Eject”
Disconnect from Your Cloud Storage Devices
Some ransomware variants may be able to take control of software that manages data saved in your cloud storage. As a result, internet attacks like Supersuso could infect the information. As a result, you should log out of any cloud storage accounts you have in your browsers and other software. You should also uninstall the cloud-management application installed on your computer until the threat has been eliminated.
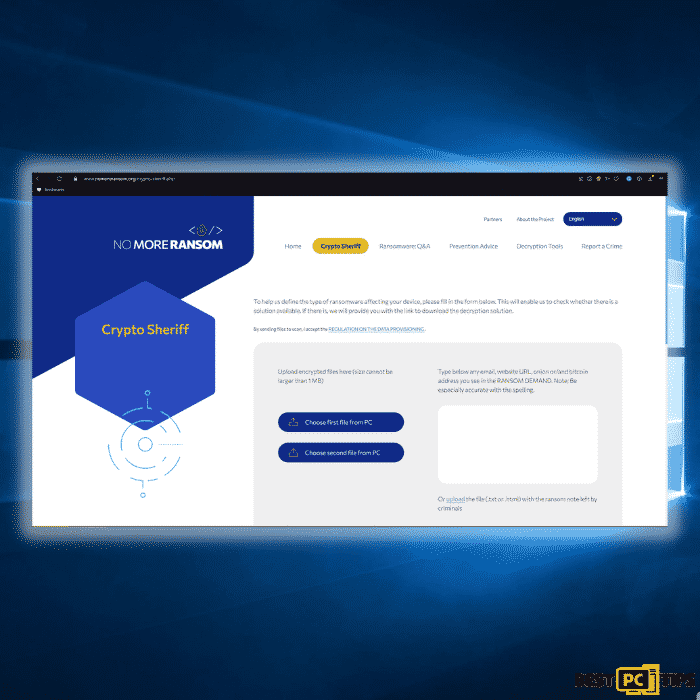
Look for a Decryption Tool for Supersuso Ransomware
Most ransomware-type attacks use incredibly advanced encryption methods, and only the developer can restore the encrypted data. This is due to the fact that decryption needs the usage of a unique key that is only generated during the encryption process. It’s difficult to recover data without the key. Instead of using the infected system as a host, fraudsters would usually store the restoration keys on a remote server.
Phobos, Dharma and other varieties of ransomware attacks are almost perfect, making data recovery impossible without the cooperation of the developers. Nevertheless, there are many ransomware viruses that are poorly created and full of loopholes. As a result, if ransomware infects your machine, you should look for available decryption programs that can effectively remove it from your computer.
It can be difficult to find the right decryption tool. As a result, we highly suggest that you use the No More Ransom Project. There is a “Decryption Tools” section on the website with a search bar. You can enter the name of the ransomware to see a list of all available decrypting tools for Supersuso Ransomware.
Keep Your Files and Data Safe
If you were able to successfully remove the Supersuso Ransomware from your computer, now is the time to back up your files to cloud storage or a removable storage device. In this way, in case your computer gets infected again then you will have all your files stored in a safe place. However, you have to remember that you should not plug your storage device or log in to your cloud storage while your computer has not yet been fully rid of any threats.
Data Backup Options
External Storage Devices – Using an external storage device and keeping it unplugged is one of the most reliable backup techniques. Please copy all your important files and data to an external storage device such as an external SSD/HDD or flash drive, then unplug it and keep it in a dry, cool location away from the sun. This strategy, however, is inefficient because data backups and upgrades must be performed frequently.
Cloud Storage Services – We recommend keeping a backup of your files with Microsoft OneDrive. OneDrive allows you to store important files and data in the cloud and sync files between your computer and mobile devices. You can also access and edit files from any Windows device and other devices with OneDrive. OneDrive allows you to save, share, and preview files, as well as see your download history, rename, move and delete files, and create new folders.
On your PC, you can make a backup of your most important folders and files. The File versioning feature will also let you keep older versions of files for up to 30 days. OneDrive has a recycle bin where you can store the deleted files for a limited period.
OneDrive offers 5 GB of free storage with subscription-based storage choices of 100 GB, 1 TB, and 6 TB available. These storage plans are available either as a standalone purchase or as part of an Office 365 subscription.
Conclusion
The best way to avoid getting infected with any online threats such as the Supersuso Ransomware is to install a reliable anti-virus tool on your computer. We suggest installing iolo System Mechanic as it not only protects your computer, it can also repair damaged files caused by the infection.
Offer
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the Supersuso Ransomware is still not fixed — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).