“Hgsh” Ransomware Removal Guide (Free Instructions)
Jessie Mullins
Issue:I can't open my files! Please HELP!
All of my files are broken. I can't open all of them. I got a ransom note from Hgsh telling me to pay them to get my files back. Is there a way to fix this? Truly appreciate any help.
The Hgsh ransomware is a harmful application that encrypts all personal data on a computer before demanding a payment to decrypt it. The threat states that paying the ransom is the only way to solve the problem, but crooks utilize a variety of techniques and methods to intimidate individuals into sending money for the supposed decryption. A strong encryption method is used by the ransomware to encrypt all of the user’s personal files, including photos, movies, documents, and archives, and to add the “.hgsh” extension in the process. There is no longer any way for victims to get their data. Cybercriminals who are behind the ransomware have a unique key that they need in order to get their data.
When the virus has finished encrypting the data, it releases a ransom note called “_readme.txt” with instructions from hackers. In order to get their files back, they must pay a ransom to get a decryption tool, according to the message. Crooks also supply email addresses such as [email protected] and [email protected] for negotiation reasons.
Here’s the full message on the ransom note:
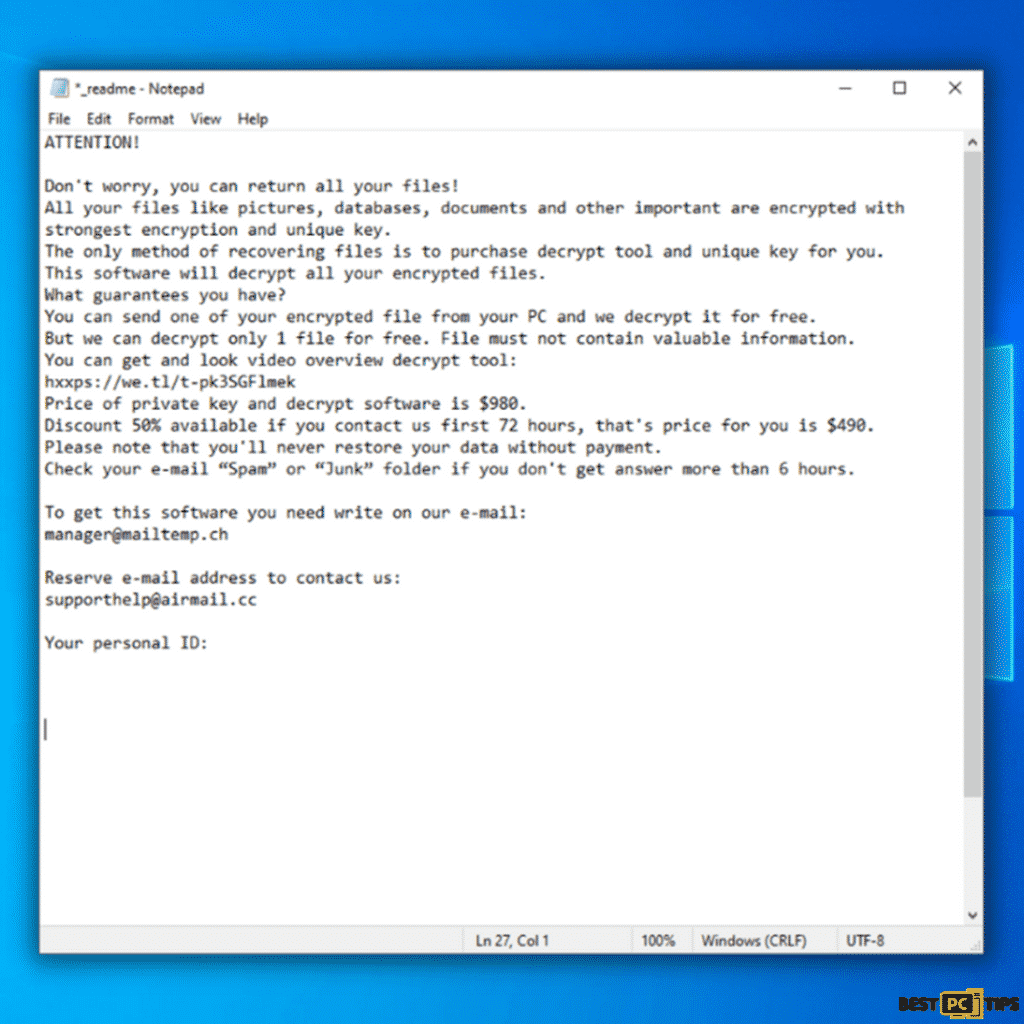
“ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with
strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-pk3SGFlmek
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
Reserve e-mail address to contact us:
[email protected] personal ID:“
A cryptovirus known as Hgsh ransomware is a member of the Djvu ransomware family of malware, which is responsible for encrypting files and demanding a ransom. This family of malware encrypts all of the critical data on a Windows machine and prevents users from accessing or seeing them in any way. All of these elements of the ransom note have remained essentially unchanged for years, despite the fact that the family of cybercriminals responsible for it is always releasing new variations.
While it is true that unlocking Hgsh virus files requires a one-of-a-kind decryption key, experts advise against paying the ransom under any circumstances. Many businesses that face file-locking threats avoid paying since cybercriminals may not follow through on their commitments, leading to financial losses. In this article, we’ll show you how to remove malware and restore data using alternate ways.
Hgsh Ransomware Threat Summary
| THREAT NAME | Hgsh Ransomware |
| Type of Threat | Files Encryptor, Cryptocurrency Virus, Ransomware |
| File Extension | .hgsh |
| Name of Ransom Note | _readme.txt |
| Amount of Ransom | Not stated, but the cybercriminals threaten on selling the victim’s information to the dark web if they are not contacted within 72 hours. |
| Contact Details of Cyber Criminal | [email protected] and [email protected] |
| Threat Symptoms and Potential Damage | Users will not be able to open the files on their system (locked files), file extensions will be replaced with .hgsh. Users will be left with a ransom note by the ransomware developer and will be demanded to pay a certain amount to recover the victim’s files. |
| Method of Distribution | Malicious ads from untrustworthy websites, downloaded torrent files from unreliable websites, Macros or Infected email attachments |
| Removal | If you think there is an infection in your system but have not yet seen the symptoms in your system, cyber security experts recommend using iolo System Mechanic to perform a holistic scan on your computer. |
Additional Details About the Hgsh Ransomware
Hgsh ransomware is a ransomware virus that infects Windows PCs through a variety of techniques. Cracks for applications and games, hacks and other pirated files are some of the more prevalent ways this family spreads. Following a successful infiltration, it employs an army-grade encryption method to encrypt all widely used data such as files and documents as well as videos, music and other types of media. Following the code change, data becomes locked and illegible. The ransom note ” readme.txt” is a direct message from the victims.
It is recommended that those who have been infected by Hgsh get in touch with the virus developers via email and disclose their personal ID. After that, consumers should receive instructions on how to proceed with the bitcoin cryptocurrency payment and eventually receive the decryption program and key for complete file recovery. The cost of the supposed decryption service varies, but this family is offering it for $490. Victims have 72 hours to respond and have their data locked before the ransom fee doubles.
We do not advocate contacting the attackers since they may not be able to provide the necessary decryption tool. Instead, have a look at the alternatives we’ve listed below. Payment may not provide access to file recovery methods but may result in virus installation or more blatant scams. Contacting criminals is not regarded as safe. Especially when these crooks are known for their deception.
Automatic Removal of Hgsh Ransomware
To limit the damage that Hgsh Ransomware might cause, make sure you use the right tools to locate and remove it. Additional viruses may infiltrate the system and launch its harmful programs, significantly degrading its overall performance. The Hgsh Ransomware can be detected early in a machine, preventing it from spreading and saving the user the trouble of removing and restoring access to their data.
Cyber security experts recommend iolo System Mechanic as one of the tools to use. This tool may do a thorough system scan and notify the user of any existing infections or other potential threats.
Hgsh Ransomware Manual Removal Instructions
If you happen to notice that your computer is infected with the Hgsh Ransomware, you have to make sure that it does not spread to other devices in your network. To do this, you have to isolate the infected device away from the other devices that are connected to your computer and the network
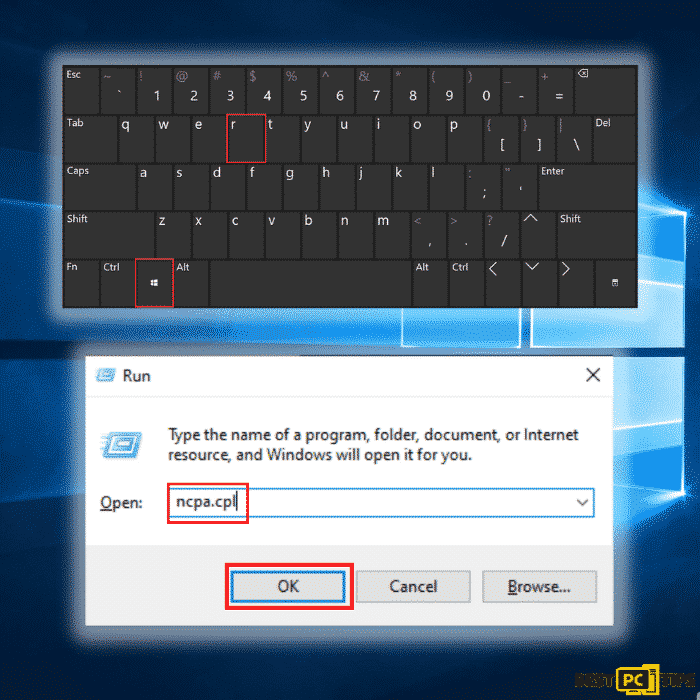
#1: Disconnect From Your Network
Step 1: Hold down the “Windows” + “R” keys and type in “ncpa.cpl” in the run command line and click “OK”
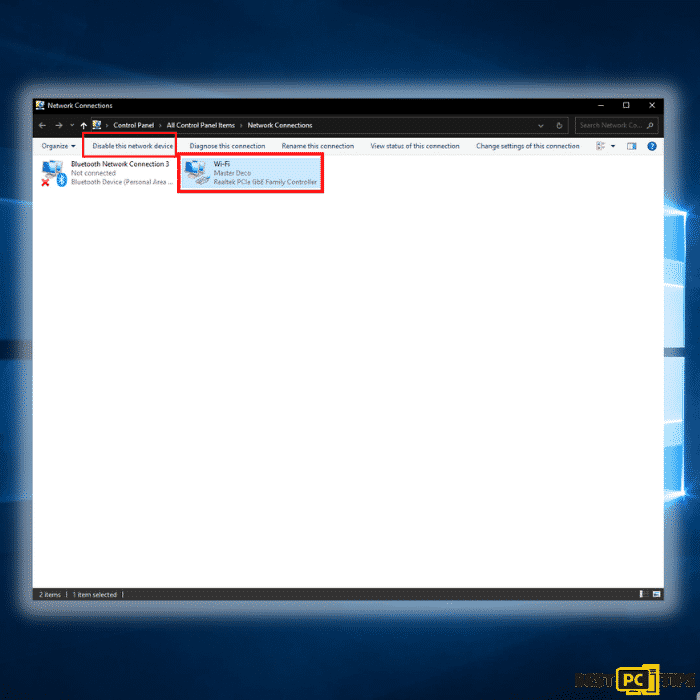
Step 2: Click on the network that you are connected to and click on “Disable this network”
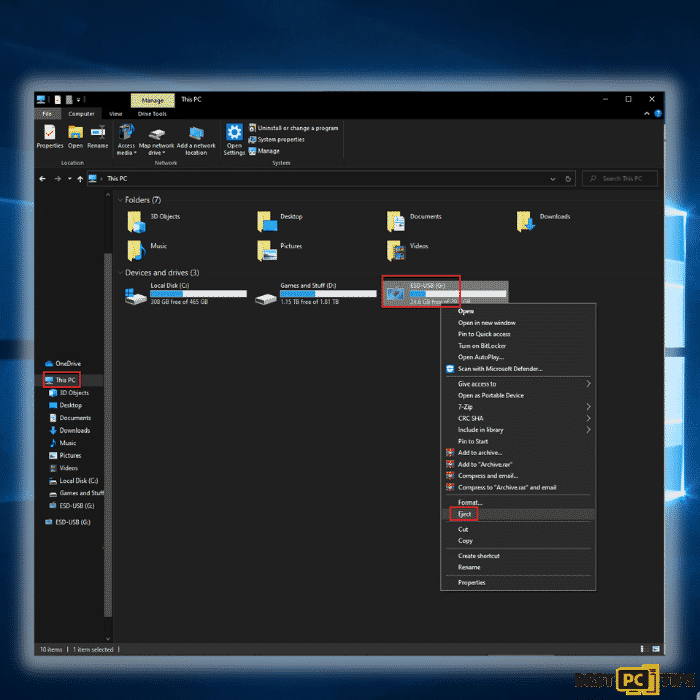
#2: Unplug All Connected Storage Devices from the Computer
The Hgsh Ransomware, as previously stated, encrypts data and infiltrates all storage devices attached to the computer. As a result, all external storage such as external hard drives, flash drives, and other similar devices should be detached as soon as possible. To avoid data corruption, we strongly encourage you to remove each device before disconnecting.
Step 1: Open “This PC” and locate all the connected storage devices. Right-click on it and click “Eject”
#3: Disconnect from Your Cloud Storage Devices
Some ransomware variants may be able to take control of software that manages data saved in your cloud storage. As a result, internet attacks like Hgsh Ransomware could infect the information. As a result, you should log out of any cloud storage accounts you have in your browsers and other software. You should also uninstall the cloud-management application installed on your computer until the threat has been eliminated.
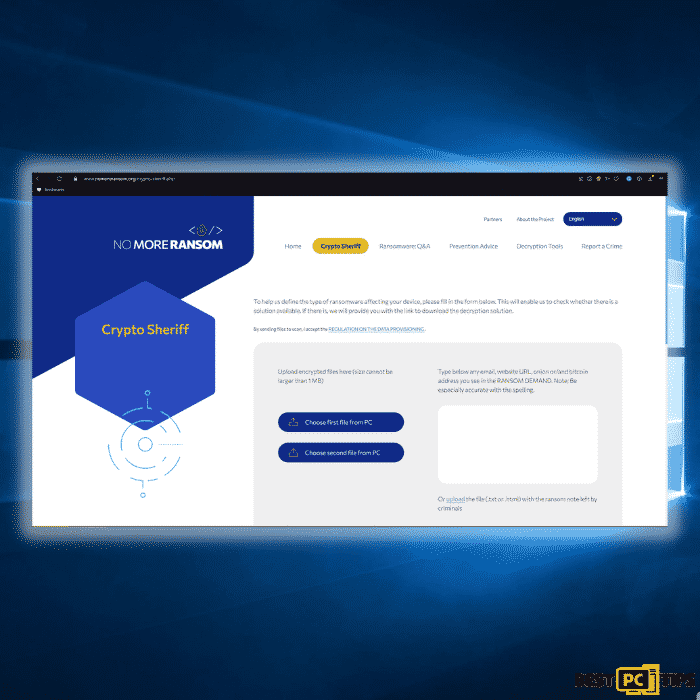
#4: Look for a Decryption Tool for the Files Infected by Hgsh Ransomware
Most ransomware-type attacks use incredibly advanced encryption methods, and only the developer can restore the encrypted data. This is due to the fact that decryption needs the usage of a unique key that is only generated during the encryption process. It’s difficult to recover data without the key. Instead of using the infected system as a host, fraudsters would usually store the restoration keys on a remote server.
Phobos, Dharma and other varieties of ransomware attacks are almost perfect, making data recovery impossible without the cooperation of the developers. Nevertheless, there are many ransomware viruses that are poorly created and full of loopholes. As a result, if ransomware infects your machine, you should look for available decryption programs that can effectively remove it from your computer.
It can be difficult to find the right decryption tool. As a result, we highly suggest that you use the No More Ransom Project. There is a “Decryption Tools” section on the website with a search bar. You can enter the name of the ransomware to see a list of all available decrypting tools for Hgsh Ransomware.
#5: Keep Your Files and Data Safe
If you were able to successfully remove the Hgsh Ransomware from your computer, now is the time to back up your files to cloud storage or a removable storage device. In this way, in case your computer gets infected again then you will have all your files stored in a safe place. However, you have to remember that you should not plug your storage device or log in to your cloud storage while your computer has not yet been fully rid of any threats.
#6: Data Backup Options
External Storage Devices – Using an external storage device and keeping it unplugged is one of the most reliable backup techniques. Please copy all your important files and data to an external storage device such as an external SSD/HDD or flash drive, then unplug it and keep it in a dry, cool location away from the sun. This strategy, however, is inefficient because data backups and upgrades must be performed frequently.
Cloud Storage Services – We recommend keeping a backup of your files with Microsoft OneDrive. OneDrive allows you to store important files and data in the cloud and sync files between your computer and mobile devices. You can also access and edit files from any Windows device and other devices with OneDrive. OneDrive allows you to save, share, and preview files, as well as see your download history, rename, move and delete files, and create new folders.
On your PC, you can make a backup of your most important folders and files. The File versioning feature will also let you keep older versions of files for up to 30 days. OneDrive has a recycle bin where you can store the deleted files for a limited period.
OneDrive offers 5 GB of free storage with subscription-based storage choices of 100 GB, 1 TB, and 6 TB available. These storage plans are available either as a standalone purchase or as part of an Office 365 subscription.
Final Words
Installing a reliable anti-virus solution on your computer is the best method to avoid becoming infected with online threats like the Hgsh Ransomware. We recommend that you install iolo System Mechanic since it not only secures your computer but may also repair any damaged files that have been created by an infection.
We also highly recommend using one of the most popular VPNs in the market – NordVPN in order to mask your identity while browsing the internet and secure your connection. It only costs a few $ per month but it makes a tremendous security difference.
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the Hgsh Ransomware is still not fixed — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).
Offer
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the Hgsh Ransomware is still not fixed — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).