How to Recover Files Encrypted by Nesa Ransomware?
Mark P.
Issue:How to recover files encrypted by Nesa ransomware?
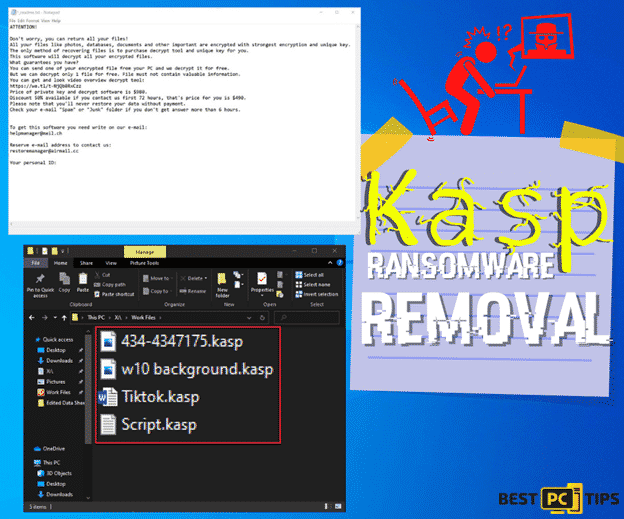
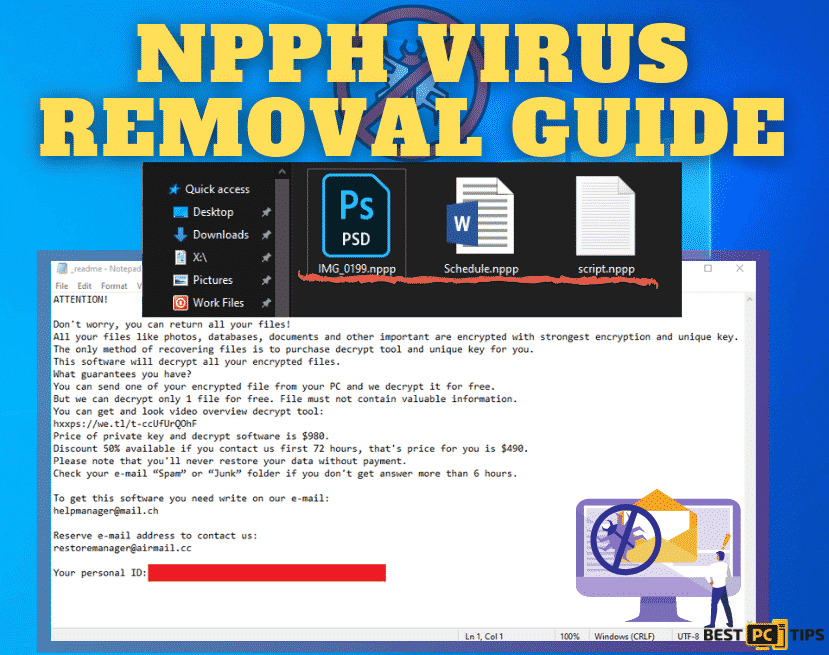
My computer got infected with a virus. All of my photos, movies, papers, and other items are corrupted. I can't get them open! The icons have been replaced with blank ones, and each file now ends in.nesa rather than.jpg,.pdf, or other extensions. How can I reclaim my files? I really need help!
The Nesa ransomware is the newest virus of the STOP/Djvu malware family. The cybercriminals behind this family are working hard to add new features and expand their operations using clever distribution tactics, so the frequency of version releases isn’t the only factor that makes it so hazardous.
Exploit kits, adware bundles, unprotected Remote Desktop connections, fraudulent updates, hacked sites, drive-by downloads, spam emails, and other methods may be used to distribute Nesa ransomware, as have previous STOP/Djvu versions. The use of several distribution vectors increases the chances of more persons getting infected with the Nesa virus, leading in a greater rate of criminal payment.
It’s is highly advised to use a VPN (we recommend NordVPN) in order to hide your online activity from the government, hackers and etc.
It will also protect you in real-time from various adware and other malicious sites that distribute viruses.
What is The Nesa Ransomware?
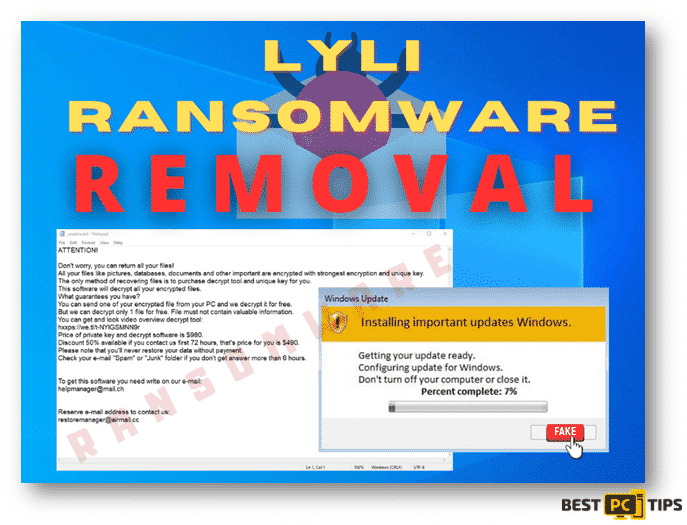
Victims are allowed to transmit one encrypted file, which the Nesa developers will decode for free. They are attempting to ‘show’ that they have tools that can decode data in this manner. These tools/keys are usually only available to ransomware creators, and it is hard to decrypt files without them.
The majority of ransomware-type malware encode data with advanced encryption techniques that are nearly hard to decrypt. Paying cyber criminals and waiting for decryption software and/or keys is the only option to unlock files. None of them can be trusted.
Victims who pay are almost certainly going to receive nothing in return. Do not put your confidence in cyber thieves to prevent getting conned. Using a backup, restore your files (only possible if data was backed up at some point prior to computer infection with ransomware).
What is the currency to pay for the ransom?
Users are usually notified of the situation via the ransom note _readme.txt, which explains that in order to retrieve the decryption tool, they must pay $980 in Bitcoin as a ransom.
But we don’t recommend doing that.
Nesa Ransomware Manual Removal Instructions
If you happen to notice that your computer is infected with Nesa Ransomware, you have to make sure that it does not spread to other devices in your network. To do this, you have to isolate the infected device away from the other devices that are connected to your computer and the network
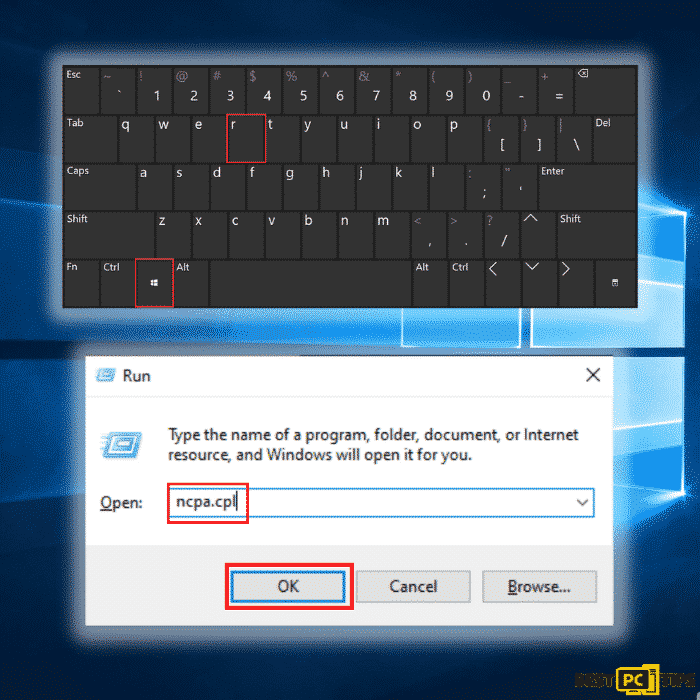
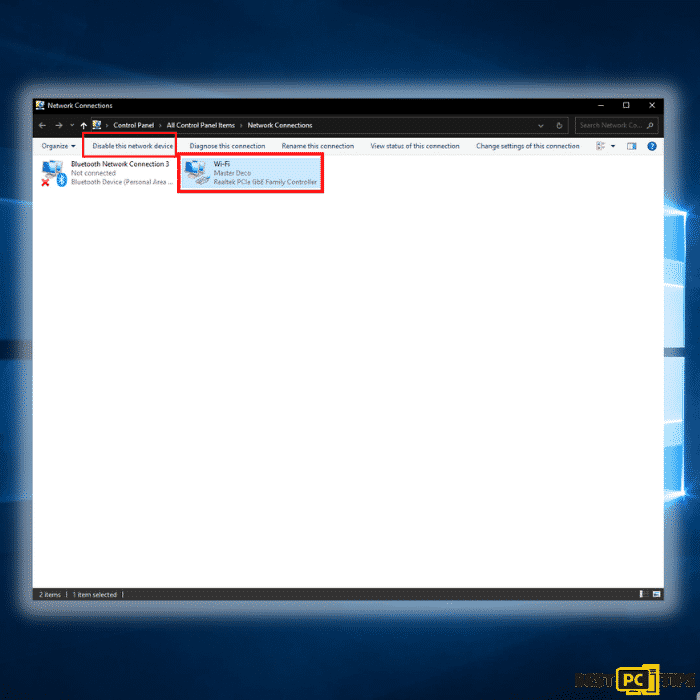
#1: Disconnect From Your Network
Step 1: Hold down the “Windows” + “R” keys and type in “ncpa.cpl” in the run command line and click “OK”
Step 2: Click on the network that you are connected to and click on “Disable this network”
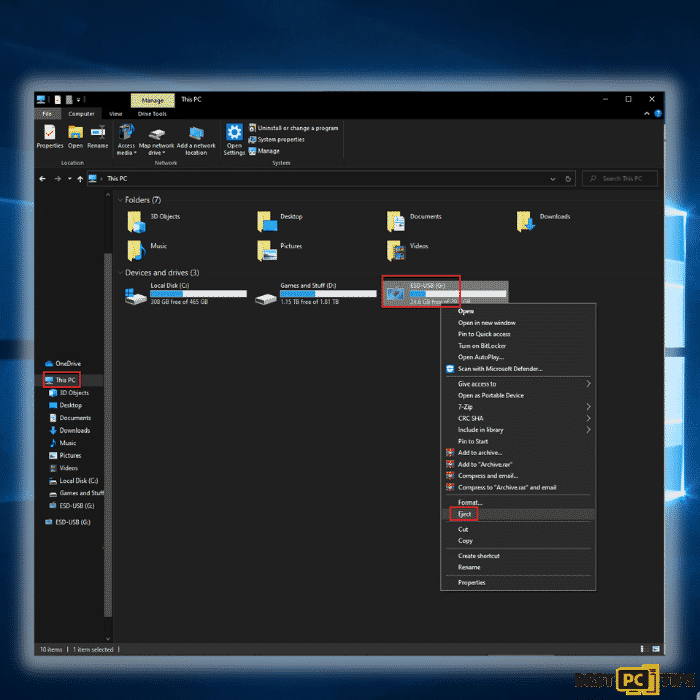
#2: Unplug All Connected Storage Devices from the Computer
The Nesa Ransomware, as previously stated, encrypts data and infiltrates all storage devices attached to the computer. As a result, all external storage such as external hard drives, flash drives, and other similar devices should be detached as soon as possible. To avoid data corruption, we strongly encourage you to remove each device before disconnecting.
Step 1: Open “This PC” and locate all the connected storage devices. Right-click on it and click “Eject”
#3: Disconnect from Your Cloud Storage Devices
Some ransomware variants may be able to take control of software that manages data saved in your cloud storage. As a result, internet attacks like Nesa Ransomware could infect the information. As a result, you should log out of any cloud storage accounts you have in your browsers and other software. You should also uninstall the cloud-management application installed on your computer until the threat has been eliminated.
#4: Look for a Decryption Tool for the Files Infected by Nesa Ransomware
Most ransomware-type attacks use incredibly advanced encryption methods, and only the developer can restore the encrypted data. This is due to the fact that decryption needs the usage of a unique key that is only generated during the encryption process. It’s difficult to recover data without the key. Instead of using the infected system as a host, fraudsters would usually store the restoration keys on a remote server.
Phobos, Dharma and other varieties of ransomware attacks are almost perfect, making data recovery impossible without the cooperation of the developers. Nevertheless, there are many ransomware viruses that are poorly created and full of loopholes. As a result, if ransomware infects your machine, you should look for available decryption programs that can effectively remove it from your computer.
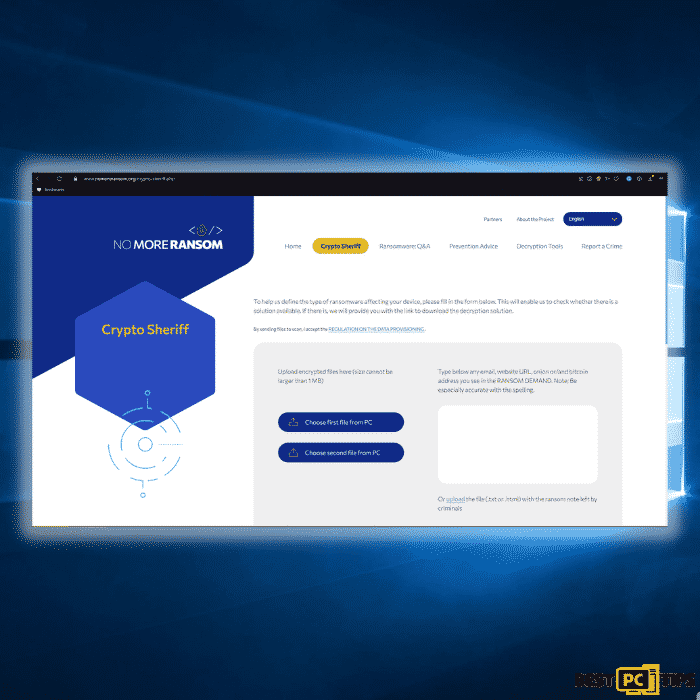
It can be difficult to find the right decryption tool. As a result, we highly suggest that you use the No More Ransom Project. There is a “Decryption Tools” section on the website with a search bar. You can enter the name of the ransomware to see a list of all available decrypting tools for Nesa Ransomware.
#5: Keep Your Files and Data Safe
If you were able to successfully remove the Nesa Ransomware from your computer, now is the time to back up your files to cloud storage or a removable storage device. In this way, in case your computer gets infected again then you will have all your files stored in a safe place. However, you have to remember that you should not plug your storage device or log in to your cloud storage while your computer has not yet been fully rid of any threats.
#6: Data Backup Options
External Storage Devices – Using an external storage device and keeping it unplugged is one of the most reliable backup techniques. Please copy all your important files and data to an external storage device such as an external SSD/HDD or flash drive, then unplug it and keep it in a dry, cool location away from the sun. This strategy, however, is inefficient because data backups and upgrades must be performed frequently.
Cloud Storage Services – We recommend keeping a backup of your files with Microsoft OneDrive. OneDrive allows you to store important files and data in the cloud and sync files between your computer and mobile devices. You can also access and edit files from any Windows device and other devices with OneDrive. OneDrive allows you to save, share, and preview files, as well as see your download history, rename, move and delete files, and create new folders.
On your PC, you can make a backup of your most important folders and files. The File versioning feature will also let you keep older versions of files for up to 30 days. OneDrive has a recycle bin where you can store the deleted files for a limited period.
OneDrive offers 5 GB of free storage with subscription-based storage choices of 100 GB, 1 TB, and 6 TB available. These storage plans are available either as a standalone purchase or as part of an Office 365 subscription.
Final Words
Now that you’ve recovered or decrypted your files on an external device, it’s time to scan your computer with antivirus and anti-malware software, or, better yet, reinstall the operating system, to completely remove any ransomware traces. Before you put files back on your computer, remember to scan your external device!
Hopefully, our guide has helped you completely removing this adware.
If you prefer automatic adware removal, we recommend downloading iolo System Mechanic.
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the Nesa Ransomware is still not fixed — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).
Offer
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the Nesa Ransomware is still not fixed — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).