How to Recover .Kvag Ransomware-Infected Files?
Jonathan S.
Issue:How to recover .Kvag ransomware files?
Please assist me. I discovered today that I am unable to open any of my files on my computer, including images that are very significant to me. Every file appears to have been replaced with a blank icon, and the file extension has been changed to.kvag. What exactly is this? Is it feasible to get my files back?
If the.kvag extension has been attached to your files, your machine has been infected with the STOP/Djvu ransomware. Ransomware infections are among the most dangerous in the wild, as they encrypt all personal information such as photos, movies, music, databases, and other files. Other infections can be removed with anti-virus software without causing major problems, while ransomware-encrypted files remain locked.
STOP ransomware was originally launched by unknown attackers in December 2017 and has since become one of the most well-known malware families in the globe. Over 150 variations of this ransomware exist at the time of writing, with Kvag being one of the most recent.
AES — asymmetric encryption algorithm – is used to secure data. It means that a secret key is used to encrypt all of the files, after which they are delivered to a Command and Control server controlled by the hackers behind the Kvag ransomware. Users require the key held by bad actors to decrypt files, and they are evidently unwilling to give it up for free.
More About the KVAG Virus and Its Methods
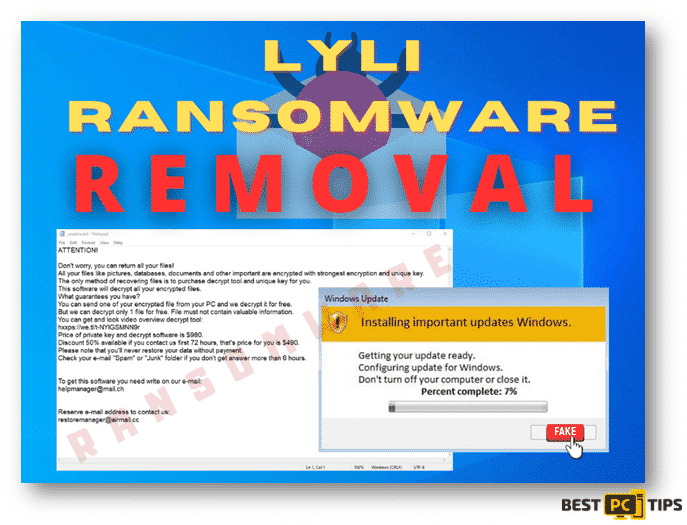
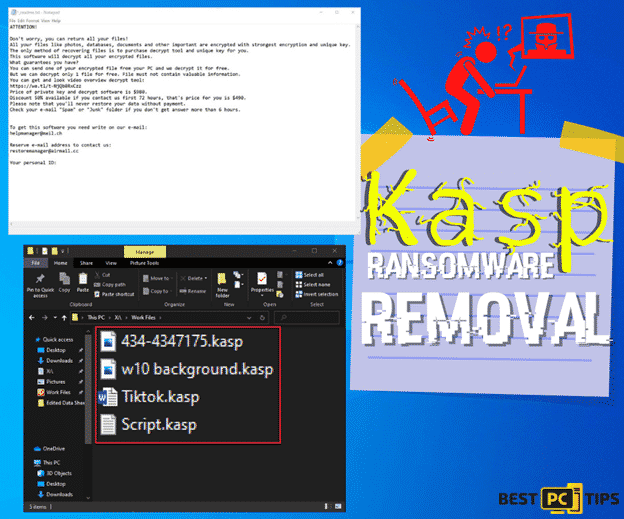
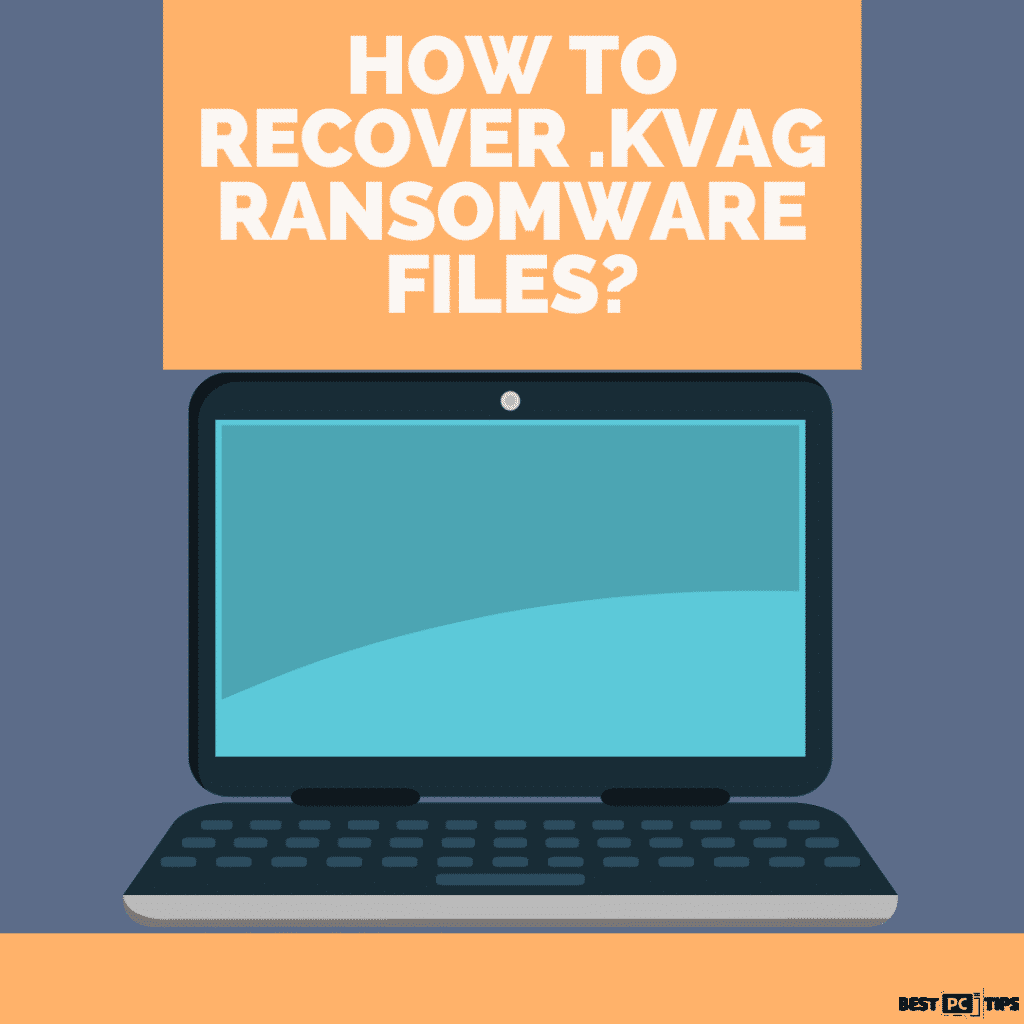
The makers of the Kvag ransomware are demanding a ransom in Bitcoin, which is normally $980. They do, however, offer a 50% discount if contact is made during the first 72 hours of infection to win users’ trust. The following is an excerpt from the ransom note _readme.txt, which is dumped into each of the encrypted file folders:
Paying a ransom is strongly discouraged because the risk of being conned remains high. Crooks are not compelled to deliver you the required key after you pay because they have already received your money. Instead, you can use the other techniques listed below to decrypt files encrypted by the Kvag ransomware.
Because its purpose is money extortion rather than OS degradation or data theft, ransomware does not hide its presence and does not touch any files that are critical to the operating system. Kvag ransomware, on the other hand, may inject multiple modules into the PC, which can spy on users’ web browser habits and steal important information, such as credit card numbers.
It is not, however, the sole reason why Kvag ransomware should be removed as quickly as feasible. If you try to recover encrypted files while the malicious payload or modules are still active, the files will be encrypted again and again, rendering the recovery procedure ineffective.
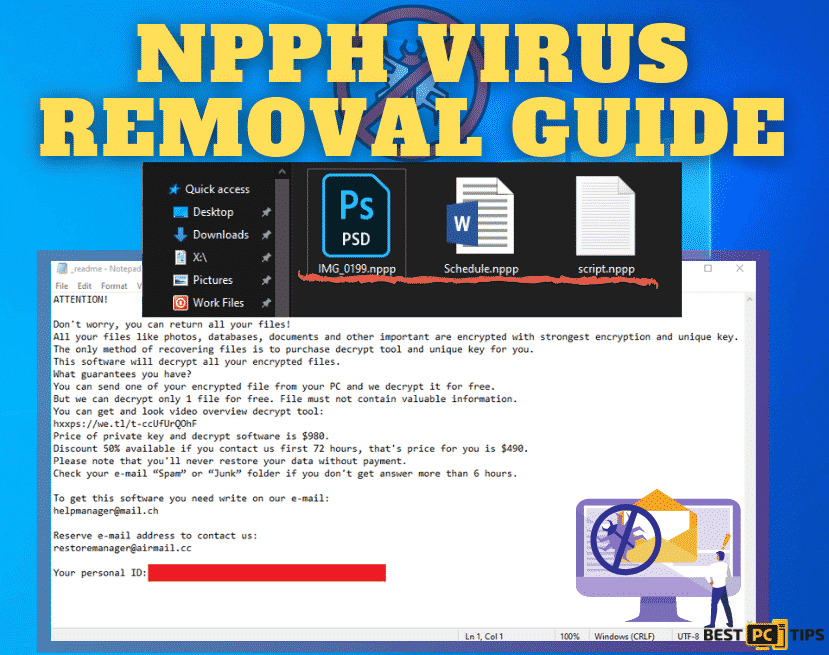
This is the ransom note you will receive:
“ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-514KtsAKtH
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e- mail:
[email protected]
Reserve e-mail address to contact us:
[email protected]
Our Telegram account:
@datarestore
Your personal ID:”
Because new versions of viruses like the Kvag virus are published so frequently, not all antivirus engines are able to identify them. Despite this, 50 antivirus engines were able to detect and remove the malware at the time of writing. The malware is known by the following names:
- Win32:Ramnit-CC [Trj]
- Trojan:Win32/CryptInject.BG!MTB
- Trojan.GenericKD.32452318
- Trojan.Ransom.Stop
- TROJ_GEN.R002C0OIE19
- Trojan.MalPack.GS, etc.
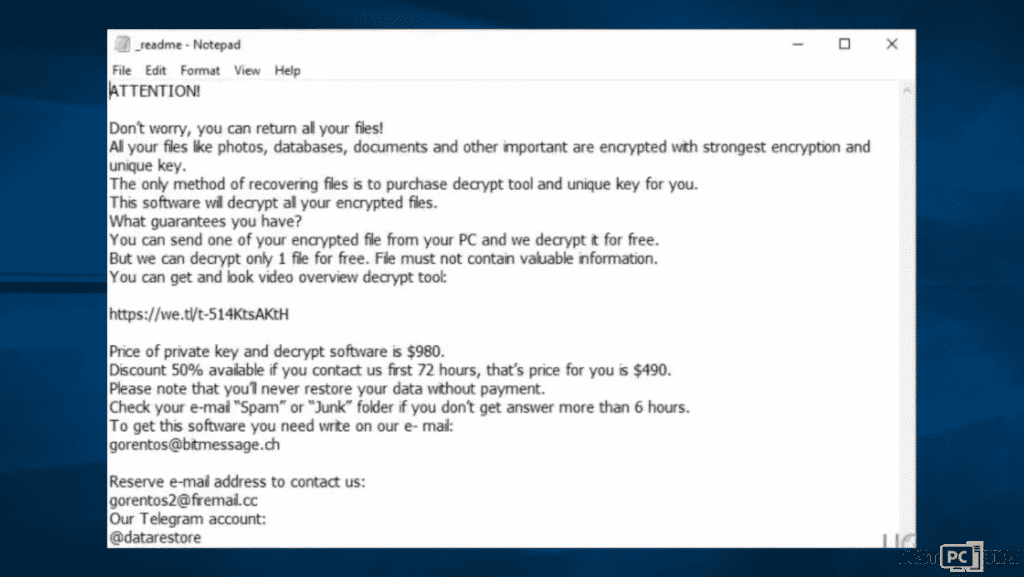
Method #1: Removal of Kvag Eansomware and Windows hosts File Prior to File Recovery
After you’ve confirmed that the infection has been removed, you may begin the file recovery process. While early versions of the STOP ransomware were relatively easy to decipher with the help of custom-made tools developed by security professionals, criminals significantly enhanced later variants. Furthermore, the Kvag ransomware can no longer be decrypted using STOPDecrypter, a tool that could recover locked files in specific circumstances.
As previously said, you must remove Kvag ransomware to ensure that the recovered data are not locked again. For this, we offer iolo System Mechanic, which can also repair malware-damaged Windows registry entries.
By changing the Windows hosts file, Kvag ransomware is known to prohibit people from accessing security sites for instructions. It may also interfere with anti-malware software while attempting to remove it. In this instance, boot into Safe Mode with Networking and run the following scan:
- Right-click on Start and pick Settings
- Click on Update & Security and select Recovery
- Find Advanced startup section and click on Restart now (this will immediately reboot your PC)
- Select Troubleshoot > Advanced settings > Startup Settings and click Restart after a restart.
- When the computer restarts, press F5 or 5 to enter Safe Mode with Networking.
- After the infection has been removed from your computer, navigate to C:Windows\System32\drivers\etc and delete the hosts file.
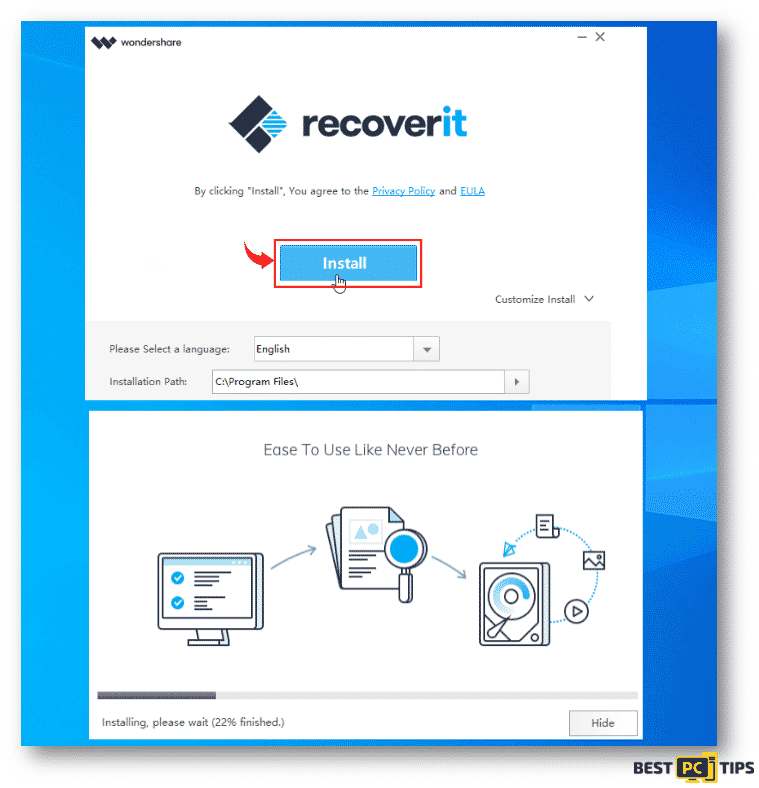
After you are done with the steps above, you are now ready to recover the files encrypted with ransomware. You will need file recovery software to help in the process in an easier way. First, download the WonderShare RecoverIT and install it on your computer. Now that you are all set for the recovery method, follow these steps:
- Open the software by hitting double click on the RecoverIT Pro shortcut.
- Perform a scan by selecting the full scan option and then click Start.
- If the scan is complete, you will see a list of files. Select the files you want to recover.
- With the files in checkmarks, you can now recover them by clicking the Recover button.
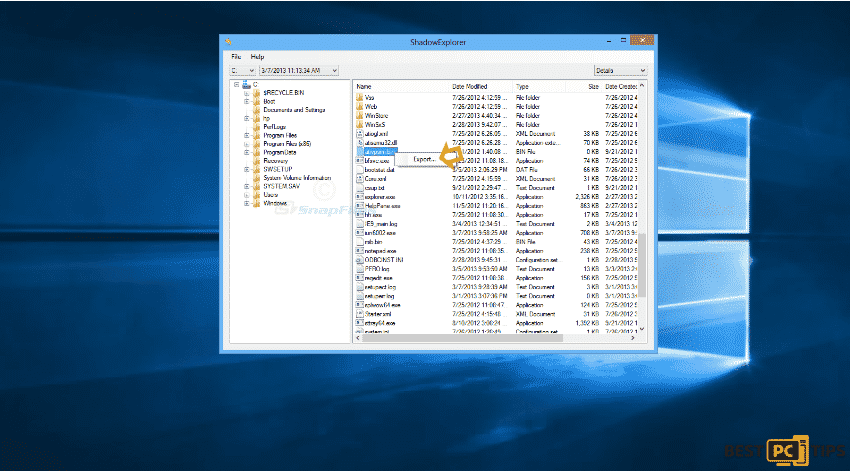
Method #3: Using ShadowExplorer to Recover Files
Since the Meds ransomware is a virus whose purpose is to delete the files stored in the Windows backup system, you will need to fix it to recover encrypted files set by Meds ransomware. In order to do this, you have to download and install the ShadowExplorer.
Follow these steps to recover your files:
- Install and setup the ShadowExplorer
- Open the application
- In the Window panel, you will see a list of files
- Select a file that you want to recover
- Right-click to enable the export option. Click export
Method #4: Use the Windows Previous Versions Feature
If you are thinking of other methods to recover lost files, there is one more. Just restore previous versions of the folder you lost to the Meds virus.
- Go to the folder in a window panel.
- Right-click the folder or file that you want to restore (The list will include files saved on a backup).
- Click previous version before you select the “Restore” button.
Automatically recover files and other system components
You can utilize free guidelines from bestpctips.com professionals to recover your data and other system components. However, if you believe you lack the necessary experience to carry out the entire recovery procedure on your own, we propose that you choose one of the recovery methods indicated in the article. We’ve already done the research on each of these programs and their efficacy, so all you have to do now is sit back and let them do the job for you.
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the .Kvag ransomware files is still not recovered — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).
Offer
iolo System Mechanic® — is a patented PC & MAC repair tool & the only program of its kind. Not only it’s a registry fix, PC optimizer, or an anti-virus/malware remover – The iolo System Mechanic® technology reverses the damage done to Windows or Mac, eliminating the need for time-consuming reinstallations & costly technician bills.
It is available for FREE. Although, for some more advanced features & 100% effective fixes you may need to purchase a full license.
If the .Kvag ransomware files is still not recovered — don’t hesitate and contact us via email, or a Facebook messenger (the blue ‘bubble’ on the bottom-right of your screen).